image.png
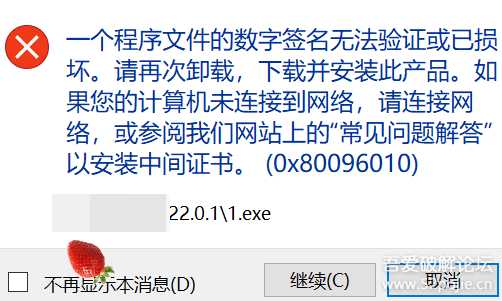
把某软件的升级检测修改后打补丁输出了;再启动时出来了这。
原来答案很简单:
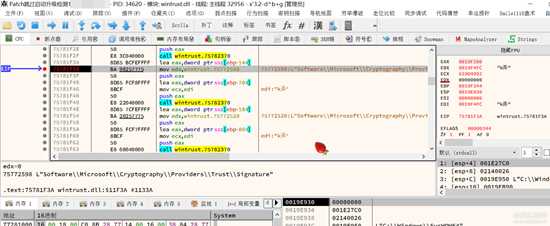
image.png
当来到这里时,慢慢向上找,或跨模块所有调用+程序领空,便能一步定位到关键代码处。
[Asm] 纯文本查看 复制代码
013FF6D1 | 8BEC | mov ebp,esp |013FF6D3 | 83E4 F8 | and esp,FFFFFFF8 |013FF6D6 | 81EC 3C070000 | sub esp,73C |013FF6DC | 803D EC135C01 00 | cmp byte ptr ds:[15C13EC],0 |013FF6E3 | 53 | push ebx |013FF6E4 | 56 | push esi | esi:"p\f)"013FF6E5 | 57 | push edi |013FF6E6 | 8BD9 | mov ebx,ecx |013FF6E8 | 0F85 EC010000 | jne patch跳过启动升级检测1_保密.13FF8DA |013FF6EE | A0 49E15701 | mov al,byte ptr ds:[157E149] |013FF6F3 | 3C FF | cmp al,FF |013FF6F5 | 75 19 | jne patch跳过启动升级检测1_保密.13FF710 |013FF6F7 | 33D2 | xor edx,edx |013FF6F9 | B9 2CA15501 | mov ecx,patch跳过启动升级检测1_保密.155A12C | 155A12C:L"SDS"013FF6FE | E8 0DFD72FF | call <patch跳过启动升级检测1_保密.sub_B2F410> |013FF703 | 3D 689AC178 | cmp eax,78C19A68 |013FF708 | 0F94C0 | sete al |013FF70B | A2 49E15701 | mov byte ptr ds:[157E149],al |013FF710 | 3C 01 | cmp al,1 | 改这里经测试不可以!013FF712 | 0F84 C2010000 | je patch跳过启动升级检测1_保密.13FF8DA | 尝试在这里跳过!013FF718 | 83CA FF | or edx,FFFFFFFF |013FF71B | 8BCB | mov ecx,ebx |013FF71D | E8 8E0473FF | call <patch跳过启动升级检测1_保密.sub_B2FBB0> |013FF722 | 85C0 | test eax,eax |013FF724 | 75 07 | jne patch跳过启动升级检测1_保密.13FF72D |013FF726 | 5F | pop edi |013FF727 | 5E | pop esi | esi:"p\f)"013FF728 | 5B | pop ebx |013FF729 | 8BE5 | mov esp,ebp |013FF72B | 5D | pop ebp |013FF72C | C3 | ret |013FF72D | 8D4424 24 | lea eax,dword ptr ss:[esp+24] |013FF731 | C74424 24 10000000 | mov dword ptr ss:[esp+24],10 |013FF739 | 894424 4C | mov dword ptr ss:[esp+4C],eax |013FF73D | 0F57C0 | xorps xmm0,xmm0 |013FF740 | 8D4424 34 | lea eax,dword ptr ss:[esp+34] |013FF744 | 66:0F134424 2C | movlpd qword ptr ss:[esp+2C],xmm0 |013FF74A | 50 | push eax |013FF74B | 8D4424 18 | lea eax,dword ptr ss:[esp+18] |013FF74F | 895C24 2C | mov dword ptr ss:[esp+2C],ebx |013FF753 | 50 | push eax |013FF754 | 6A 00 | push 0 |013FF756 | 66:0F134424 44 | movlpd qword ptr ss:[esp+44],xmm0 |013FF75C | C74424 50 00000000 | mov dword ptr ss:[esp+50],0 | [esp+50]:sub_A9DB90013FF764 | 66:0F134424 5C | movlpd qword ptr ss:[esp+5C],xmm0 |013FF76A | C74424 64 00000000 | mov dword ptr ss:[esp+64],0 |013FF772 | 66:0F134424 6C | movlpd qword ptr ss:[esp+6C],xmm0 |013FF778 | C74424 40 34000000 | mov dword ptr ss:[esp+40],34 | [esp+40]:"p\f)", 34:'4'013FF780 | C74424 4C 02000000 | mov dword ptr ss:[esp+4C],2 |013FF788 | C74424 54 01000000 | mov dword ptr ss:[esp+54],1 | [esp+54]:sub_A9DB90013FF790 | C74424 68 10000000 | mov dword ptr ss:[esp+68],10 | [esp+68]:&"0嫨"013FF798 | C74424 20 6BC5AA00 | mov dword ptr ss:[esp+20],<patch跳过启动升级检测1_保密 | [esp+20]:L"燐豺"013FF7A0 | C74424 24 44CDD011 | mov dword ptr ss:[esp+24],11D0CD44 |013FF7A8 | C74424 28 8CC200C0 | mov dword ptr ss:[esp+28],C000C28C |013FF7B0 | C74424 2C 4FC295EE | mov dword ptr ss:[esp+2C],EE95C24F |013FF7B8 | FF15 704A4B01 | call dword ptr ds:[<&WinVerifyTrust>] ==>此处是数字签名校验的源头(1)修改之后启动文件被修改的提示就没了!
标签:
2021年遗留问题:数字签名
免责声明:本站文章均来自网站采集或用户投稿,网站不提供任何软件下载或自行开发的软件!
如有用户或公司发现本站内容信息存在侵权行为,请邮件告知! 858582#qq.com
狼山资源网 Copyright www.pvsay.com
暂无“2021年遗留问题:数字签名”评论...
